Single WAF. One Policy. Works Across Every CDN.
The first WAF that runs across all your CDNs, powered by CheckPoint. Identical policies, ML-driven protection, and centralized control, without rewrites or vendor lock-in.

%201.avif)









.png)
.png)

%201.avif)









.png)
.png)

%201.avif)









.png)
.png)
SECURITY COVERAGE
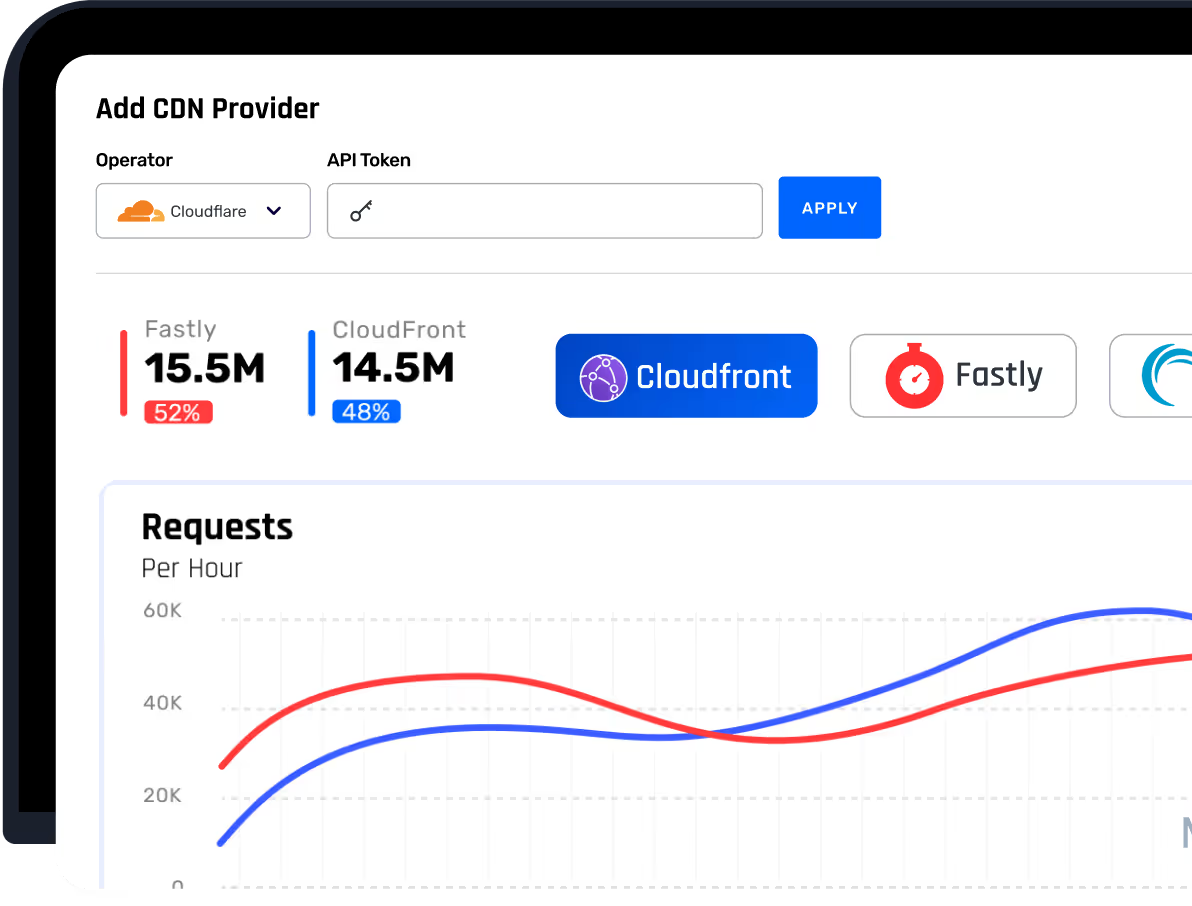
Consistent Security Across Every Provider
Consistent Security Across Every Provider
IO River’s unfied security layer runs at the edge of every connected provider, enforcing the same security logic regardless of where traffic is routed.


Write Once. Enforce Everywhere.
Define WAF rules and train ML model a single time and apply rules uniformly across your entire edge footprint.
Security That Survives Outages
WAF enforcement remains active even when providers degrade, fail, or shift traffic unexpectedly.


Security Without Operational Sprawl
Manage routing, WAF policies, logs, and analytics from one unified control layer.
Powered By
Check point WAF
Powered by Check Point WAF
IO River’s Unified Security layer is built on Check Point WAF, an enterprise-grade security engine backed by over 30 years of cybersecurity leadership.
Enterprise-Grade Threat Prevention
Check Point WAF delivers advanced threat prevention, continuously updated protections, and multi-layered defense applied consistently across every edge provider.
AI-Driven Detection
Prevention-first, AI/ML-driven protection that automatically blocks known and unknown threats for web, API, and AI applications-including zero-day attacks, OWASP Top 10 risks, API abuse, and bots directly at the edge before malicious traffic reaches applications.


Recognized by
Leading Industry Analysts
Built for Streaming At Scale
Multi-CDN Application Security
Learn how IO River and Check Point deliver ML-driven application security consistently across every CDN in your stack.

WE SOLVE REAL PROBLEMs. FOR REAL PEOPLE.
Who is the IO River SEcurity Solution for?
Platform & SRE Teams
Who need consistent security without slowing down traffic engineering.
Security Teams
Who want ML-driven protection without managing multiple WAF stacks.
Multi-CDN Architectures
Where downtime, breaches, or policy drift are unacceptable & security must be consistent, auditable, & edge-enforced.
High-Risk & Regulated Applications
Where downtime, breaches, or policy drift are unacceptable & security must be consistent, auditable, & edge-enforced.
Secure Every Edge. Operate One System.
Run application security the same way you run delivery: unified, resilient, and under your control.