Check Point Rule-based WAF
Rule-based WAF
In addition to the ML-based engine, the Check Point powered WAF also includes a standard engine called Intrusion Prevention (IPS) that can prevent suspicious activity based on rules. IPS provides protection for over 2800 web-based CVEs (Common Vulnerabilities and Exposures), such as OWASP Top 10, as well as rules designed and maintained by Check Point. The signatures arrive automatically to agents/gateways as soon as Check Point Security Research team releases them. For example, IPS protects against SQL injection, path traversal, LDAP injection, evasion techniques, illegal HTTP methods, Log4Shell, Text4Shell, and MOVEit-related attacks.
One specific benefit of these signatures is the ability to see logs that indicate a specific CVE number.
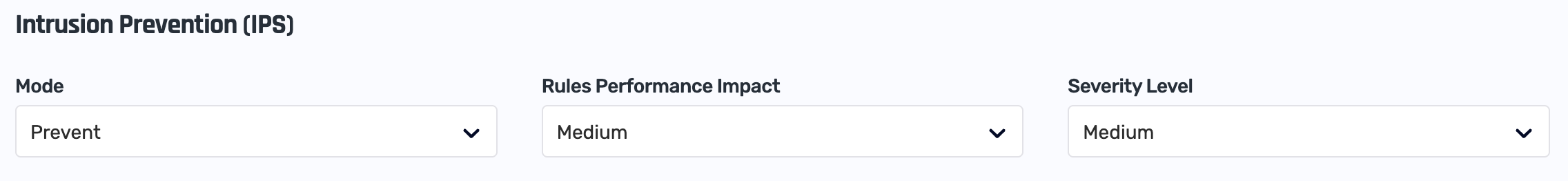
Like the ML-based engine, the rule-based engine can be set into different modes of operation:
- Learn: this is the initial mode where the engine does not block any traffic
- Prevent: in this mode the engine blocks traffic based on its rule set
- Disabled: you can completely disable the rule-based engine
Rules Included
IPS includes rules such as the OWASP Top 10:
- Broken Access Control, for example:
- Bypassing access control checks by modifying the URL (parameter tampering or force browsing)
- Elevation of privilege
- CORS misconfiguration
- Force browsing (guessing URLs)
- Security Misconfiguration
- Missing appropriate security hardening
- Lack of security headers or directives, or they are not set to secure values
- Injection, such as:
- SQL injection
- OS command injection
- LDAP injection
- Authentication Failures
- Credential stuffing with/out password spray attacks
- Weak or well-known passwords
- Exposed session identifier in the URL, a hidden field, or another insecure location
Configuration
IPS Overhead
The engine comes with a large set of rules, classified by their severity level and confidence.
You can control which rules are examined (i.e. activated) in order to control the performance impact on your traffic. Activating more rules increases CPU usage, as each rule must be evaluated per request.
You can control this in two ways:
- Set the performance impact you're willing to sustain, ranging from Low (activate fewer rules) to High (activate more rules).
- Set the rules' severity level, ranging from High (active only rules for high-severity threats, i.e. fewer rules) to Low (active all rules, i.e. fewer rules)
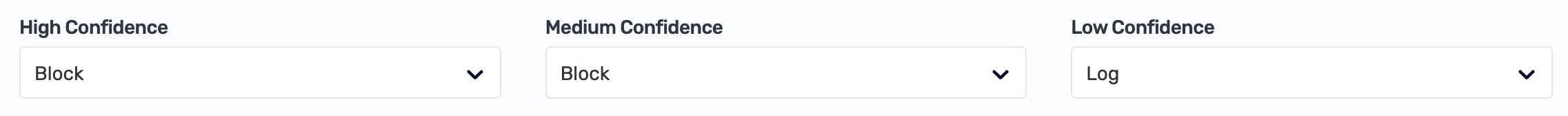
IPS Threat Prevention and Confidence Levels
While the engine is in Learn mode it does not block any traffic, but rather add suspicious activity to the sampled logs of the WAF engine.
Once the engine is set to Prevent mode, you can control which rules are included by setting its behavior for rules of High Confidence, Medium Confidence, and Low Confidence. We suggest beginning with prevention of rules with High Confidence.